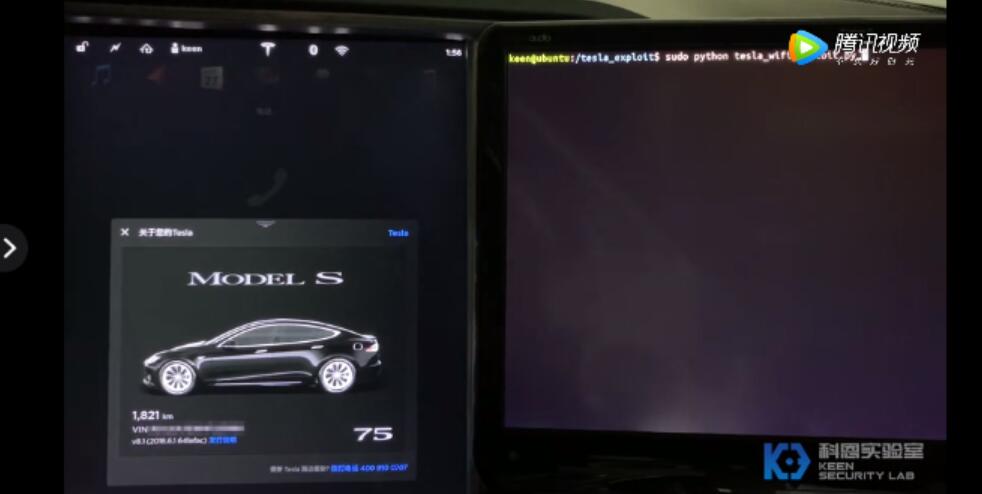
Tencent Keen Security Lab said on Thursday that their engineers have been able to remotely hack into Tesla's in-vehicle system through wireless protocols.
The lab said in a post that in order to better understand the security of Tesla's in-vehicle system, it researched the wireless function module (Parrot module on Model S) and found two vulnerabilities.
One is in the wireless chip firmware, and the other is in the wireless chip driver. By combining these two vulnerabilities, an attacker can execute arbitrary commands in the Linux system of the Parrot module.
In other words, through these two vulnerabilities, an attacker can remotely penetrate Tesla's vehicle system through wireless protocols.
In the past two years, Tencent Keen Lab has demonstrated how to penetrate Tesla's CID, IC, gateway, and autonomous driving modules.
This process takes advantage of multiple vulnerabilities in the kernel, browser, MCU firmware, UDS protocol, and OTA updates.
They also analyzed the specific implementation details of the automatic wiper and lane recognition functions and attempted to attack the defects in the real world.
The Keen Lab reported two vulnerabilities to Tesla in March 2019, and Tesla has fixed the vulnerability in the 2019.36.2 release. At the same time, Marvell also fixed the vulnerability and issued a security bulletin for the vulnerability.
You can click here for the full report.
Tesla said on Thursday that it will deliver the second batch of China-made Model 3 sedans to customers at the Shanghai plant on January 7.
On December 30, the China-made Tesla Model 3 was officially delivered to customers in the Shanghai Super Factory, which indicates that the Shanghai Super Factory has fully entered the production and delivery state.